Checking the Security of a Crypto Wallet - Taking KryptoGO Wallet as an example
2022-01-24
Recommend Articles
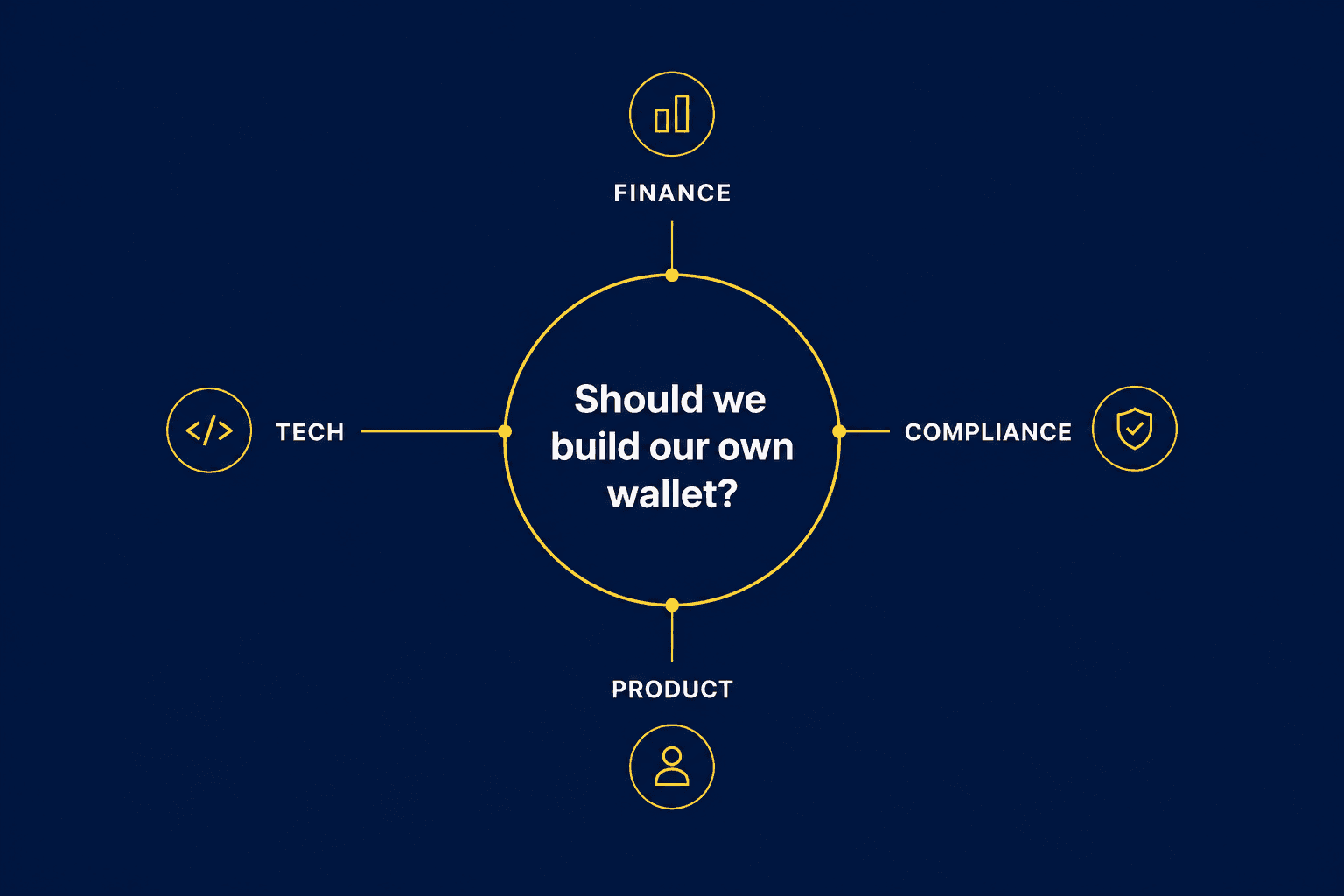
Where White-Label Wallet Projects Actually Get Stuck

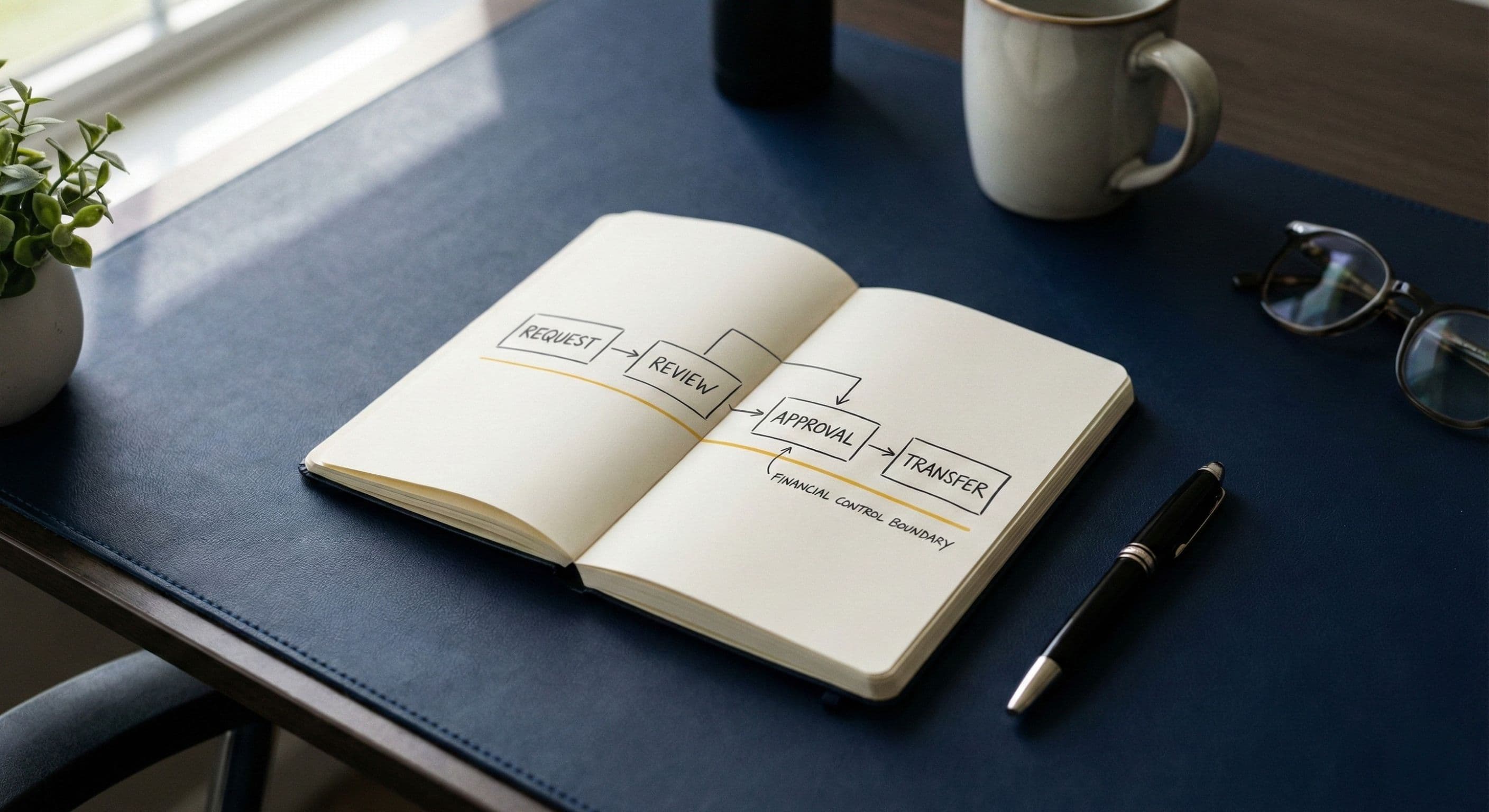
How Mining Farms Use Stablecoins for Electricity Payments: From Collection to Compliance

What Are KYC, KYB, and KYA? What Businesses Actually Need to Check When Using Virtual Assets
Hot Articles
From 2,000 BTC to Enterprise Treasury Risk
Hot Tags
HotNewsNFTBlockchainDeFiSecurityComplianceUpdates






